 Serious programming in the olden days mean to deal with Unix – the father of today’s ubiquitous Linux running bigger part of the internet.
Serious programming in the olden days mean to deal with Unix – the father of today’s ubiquitous Linux running bigger part of the internet.
The first bigger project I was involved in was still the good old DOS with Turbo Pascal – anybody remember that?
As soon as I could, and we had to build something less of a hack but more of a software-engineered application, I steered my client into Unix, first the X86 version of Xenix, which turned out to be too flaky, and then a nice hundred thousand dollar HP Workstation. As it was an application involving graphics, an important order of business was to get familiar with the principles and techniques of the X11 windowing system.
This was not a very long-lived project and with the advent of more powerful x86 hardware and a finally decent piece of software from Microsoft – Windows NT – the develoment was moved to that new platform. The fact that the port from X to NT was not terribly difficult was a nice testimonial for proper application of software engineering principles. Hacking mentality as promoted by something like Turbo Pascal would have required a complete rewrite.
System administration, I had become familiar with during that time, was helpful when I started to maintain a few linux web servers years later. I always considered X11 far superior to all the other graphical windows software but I really had never anything to do with it any more – until a point in time a few days ago.
First of all, I finally succeeded in getting Ubuntu running on an old laptop. A flaky DVD had never gotten me through an installation properly and the machine was so old that it could not boot from a memory stick. I ultimately succeeded when I found a utility I could burn on a CD and boot from that made my USB bootable. Now I could load Ubuntu from the USB stick.
So, there I finally was again with a computer with a proper graphical user interface. But that computer was tucked away somewhere with little physical access. It serve as a local testing machine for web development – did not really need that X Windows for that!
But it was sitting there, teasing me, so I finally got XMing – an X Server running on MS Windows – installed on my main computer where I sit all day and I could finally connect to that old laptop remotely with a graphical user interface. In my early days of X11 there was not too much concern about security – it was all on the local network – yes, a coax ethernet cable – and to have an application display on an xterminal you just had to set the DISPLAY environment variable to the IP address of any X-Server, like a xterminal, and authorize its use.
That is all different now. I learned that from a remote machine you start an ssh connection on my workstation (windows 7) to the remote host (old linux laptop) using putty. If the putty session had X Forwarding enabled then a secure tunnel for all the X traffic was created. This tunnel could even go through a router with NAT without a problem. Initially I had wondered why I saw the value of the DISPLAY variable set to strange things like localhost:10.0 – but I finally understood that this was how the ssh tunnel worked: the ssh server on the old laptop pretended to be a local X server on display number 10; then it transported all the X traffic it received securely to the machine I was sitting on and fed it into XMing. It all worked perfectly.
Two weeks later I received my first Raspberry Pi and that little wonder did behave the same way as the old laptop, a bit slower I have to admit, so the old laptop is still a bit more powerful than the miniature linux box sitting over there on my speaker. Both are full LAMP systems and are even accessible from the rest of the world through the magic of DynDNS and port forwarding.
But then my trouble began.
As I had all this so nicely and easily set up, it was suddenly not enough any more that I logged into my real web servers only with putty, SCP, and DirectAdmin. Nostalgia had me in its grip and I just had to get X running on them as well.
First of all there was no X-stuff installed on those servers as they were web servers in some remote data center. But a “yum install xterm” got this handled. Still no go – starting xterm from the ssh login gave me the error message that the display was either not there or could not be opened.
The next step, I found out, was to enable X11Forwarding for the sshd on the remote server – but still no go – the DISPLAY variable was still not set. Lots of Googling around but no solution – everything I tried made no difference.
But I learned about the -vvv parameter to ssh. It would give me insight into what was happening during the establishing of the ssh connection. Unfortunately, putty does not have it! But I found that it has a logging function and after turning this on and comparing the logs from connections to my local old laptop and the remote web server I finally saw the light:
xauth
After I had it yum-installed and run to generate a new .Xauthority file for a local X server my quest for the xterm running on that web server and displaying on my local machine behind a NAT router in my office had come to a successful conclusion.
Not that I will use that much – putty and SCP have done the job for me for years – but I now could, potentially, install firefox on that server and start browsing through that server located at a very different place on the planet.
Hmmm – why don’t I just try that: yum install firefox……………………….
finally, after installing a gazillion dependent packages, the installation is – complete!
Now: firefox& – wait – wait – wait…
But it is clear that I have to file this away under ‘education’ as it is so slow to make it more or less unusable.

 Today the wait was over – the second half of season 7 of Dr. Who has started.
Today the wait was over – the second half of season 7 of Dr. Who has started. This is history as we made it!
This is history as we made it! Serious programming in the olden days mean to deal with Unix – the father of today’s ubiquitous Linux running bigger part of the internet.
Serious programming in the olden days mean to deal with Unix – the father of today’s ubiquitous Linux running bigger part of the internet.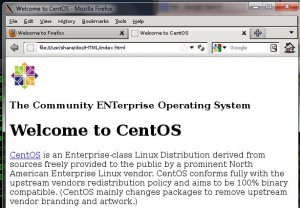

 This is only the second time that one of my site was hacked – not bad for how long I am doing this type of stuff.
This is only the second time that one of my site was hacked – not bad for how long I am doing this type of stuff.